A customer of mine is using Trend Micro as their security suite. They found out that Windows Defender for Server was still running actively, and they wanted to have it in passive mode. I couldn’t find a blog that contained all the steps. So, I decided to write it down myself.
This is the article from Trend Micro.
https://cloudone.trendmicro.com/docs/workload-security/anti-malware-windows-defender/
Prerequisites
To use passive mode for Windows Defender for Server you must onboard them to Defender for Endpoint:

Source: Microsoft
Set Windows Defender for Server Passive mode
So, it’s now time to set the passive mode. Firstly, we need to check the current status of Windows Defender. Use this command:
Get-MpComputerStatus
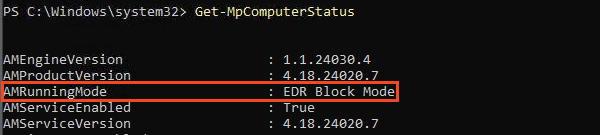
This is probably your current result if you are reading this post:

After that, we first need to set a registry key to set the passive mode for Windows Defender. The Microsoft docs explicitly specify this, don’t skip this part. This is the registry key:

You can also set this key via group policy:
Computer Configuration > Administrative Templates > Windows Components > Windows Defender ATP:
Turn on Windows Defender AVD passive mode = Enabled

The next step is to onboard the device to Microsoft Defender for Endpoint. You can do so by downloading the onboarding package from the security portal.
Log on to the security portal and go to Settings > Endpoint > Onboarding > Select the correct OS:

After that, run the WindowsDefenderATPLocalOnboardingScript.cmd on the machine that you want to onboard.
You see the machine in the security portal:

Next, run this command again:
Get-MpComputerStatus
On my machine, this status (EDR Block mode) was returned by running the command above. This was not expected. I wanted to see “Passive Mode”.
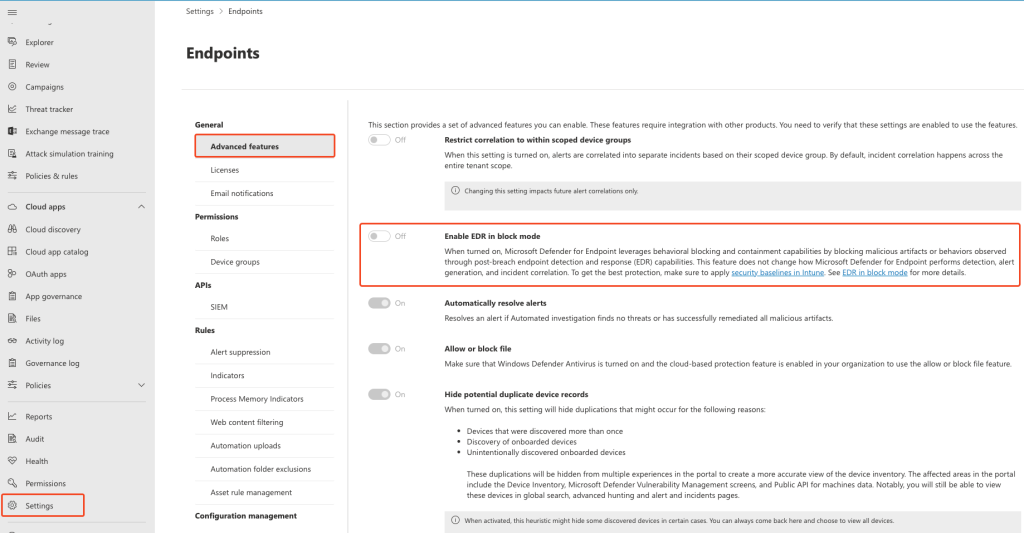
So, I set out googling again and found out that you need to disable “EDR Block Mode” in the Defender portal:
(Settings > Endpoints > Advanced Features > Enable EDR in Block mode)
Lastly, we run the command again
Get-MpComputerStatus
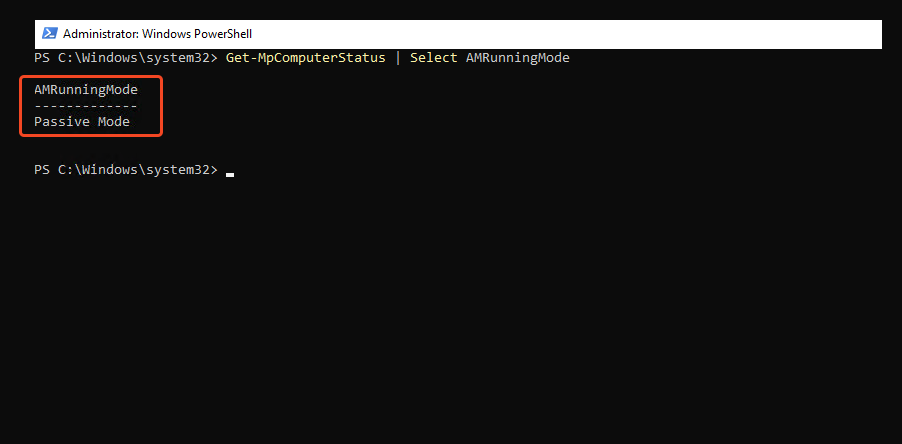
After that, the correct result is returned:
Other posts: