New year, new blog! This post is all about how to view API permissions for all Service Principals. It is quite easy to see the permissions for 1 Service Principal but how about all? I created a script that gathers all assigned application permissions and exports them to CSV (or you can use Out-Gridview).
A customer of mine asked to create this script because we are implementing Conditional Access for Service Principals (Workload identities). Read about that here.
And we wanted to know what our most highly privileged service principals are. This gives you an idea of the biggest attack vector and what service principals you must protect first! Furthermore, It might also give you an idea of which privileges to remove from which service principals.
So, what do I do? Yes, we go to Powershell, write a script, and gather all the information. And, most importantly, I share it on my blog for everybody to use. (To my knowledge, it is not possible to this from the GUI)
Prerequisites
You must the Az.Accounts Powershell module installed. It is only needed for gathering an Access Token. So, if you have another way, you can remove this.
The script
You can find the script on my Github.
At the top of the script is a function that does the Graph API request. It contains paging. So, If you have more than 100 results it will loop through the pages. (You can use this function for any graph request, it is very handy)
When you first run the script it opens a web browser that asks you to log on to your Azure tenant. It then uses the Access Token to perform the Graph API requests.
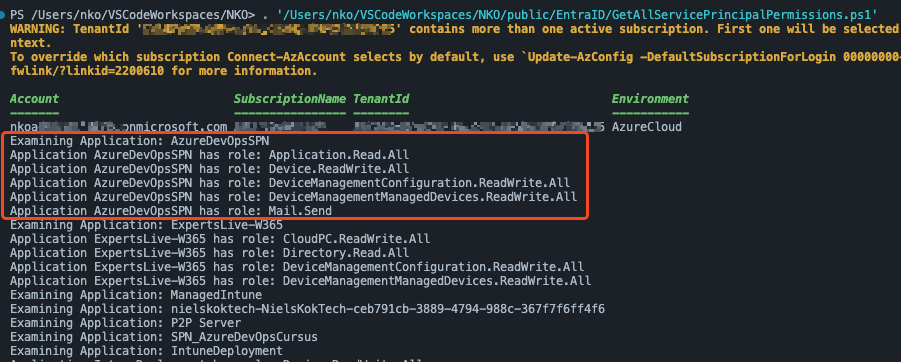
Below you can see the first output, it logs on and then shows the application it is examining and what API permissions it has.
After that, it exports all data to a CSV file:

Other Posts:
Monitoring AVD with Azure Monitor
Windows Autopatch – Deployment Cadence
Ouch, += is a cardinal sin 😉
Haha, will adjust it.
Really like all your posts – Great content and awesome delivery!
Hi Cheri,
Thanks!